Security Researcher 🔓

My name is Vladimir Smitka and I’m a security researcher/hobbyist from the Czech Republic. I specialize in WordPress security&performace and secure infrastructure for running websites. I do massive scans of the internet for my research. I’m also the owner of Lynt, a PPC Agency and Spirit Radar, a global service for tracking prices of Rums and Whiskies. I’m also an active member of the Czech WordPress community and one of the WordCamp Prague organizers. For a quick understanding of my approach, check out my WordCamp EU security talk.
Blog
Latest articles on bugs found, scan results and tips.
-
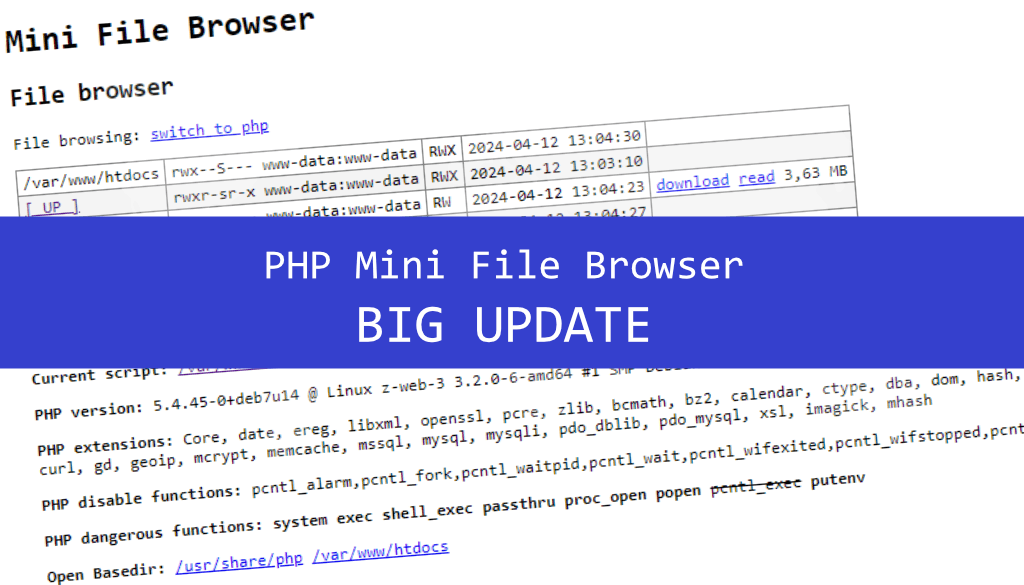
PHP Mini File Browser Update
Read more: PHP Mini File Browser UpdateWhen testing the security of PHP/WordPress sites, I am usually first interested in the environment where the site runs and the structure of the application. To simplify the initial audit, I wrote a mini PHP file browser for myself in 2014 (I put it on GitHub in 2016). Since then, there have been only few…
-

13 extra things we do for better WordPress Security
Read more: 13 extra things we do for better WordPress SecurityLooking beyond basic tips, here are 13 extra measures based on years of experience to fortify your WordPress security.
-
WordPress Builders: journey from phpinfo() to RCE
Read more: WordPress Builders: journey from phpinfo() to RCEIn the context of the recent surge in attention towards a critical Remote Code Execution (RCE) flaw in Brick Builder, I want to shed light on a less-known issue I discovered and reported two years ago. This flaw, which has been quietly addressed in versions around 1.6, affects not only Brick Builder but also other…
-
Hello, Unauthenticated RCE here! What to do?
Read more: Hello, Unauthenticated RCE here! What to do?Last week we witnessed a critical vulnerability in the WordPress visual builder Bricks: https://snicco.io/vulnerability-disclosure/bricks/unauthenticated-rce-in-bricks-1-9-6. In this article I will describe how the attack happened, add a bit of theory for those who are not so tech-savvy, add procedures for cleaning up the site and tips for preventing future attacks. What happened? Due to the severity…
-

WordPress installer attack race
Read more: WordPress installer attack race“The Famous WordPress 5-Minute Install” was great. Unfortunately, today it can cause serious security problems. The typical scenario is to upload core files to your host, open the installer, and it is done in a few minutes. During these few minutes is your installer publicly available to everyone. If the attacker is speedy enough, he…
-
WordCamp EU – Q&A
Read more: WordCamp EU – Q&AHow do I know that my PHP or Apache version is vulnerable? You can find vulnerabilities for the particular version on CVE details. You should use the lastest versions of server components, currently: Also keep in mind, that every PHP major versions is fully supported only 2 years. For example PHP 7.1 is at the…
-

Global scan – exposed .git repos
Read more: Global scan – exposed .git reposAt the beginning of July 2018, I decided to do some research on Czech websites to find out how many are not properly configured and allow access to the .git folder within the file versions repository. There were many of these sites in my database from the previous security scans and I was curious about…
-

Python & Ruby webserver config – the great misunderstanding
Read more: Python & Ruby webserver config – the great misunderstandingTwo months ago I ran a huge global scan for unintentionally exposed .git repositories. I was surprised to find many Python and Ruby applications with this issue. The total number wasn’t very high – around two thousand, but when I normalized it according to the market share of these programming languages, the situation was worse…
-

Enhance your CentOS security for $1 a month with autoupdates
Read more: Enhance your CentOS security for $1 a month with autoupdatesHow to enable security autoupdates properly on CentOS and why are the most tutorials wrong.
Subscribe
Enter your email below to receive updates.